The face of an opportunity
The ID management business sparkles with high expectations, but is it still in a hurry-up-and-wait mode?
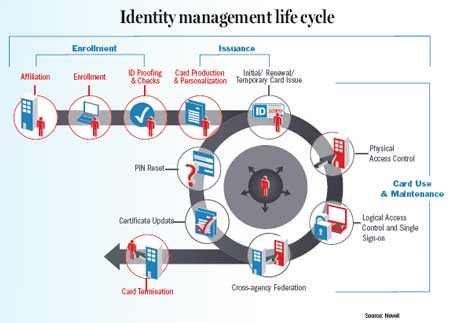
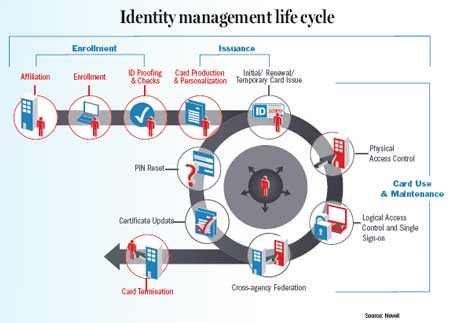
The anticipated businessboom in government identity managementsystems is taking longerto arrive than some had expected.Sustained growth in spending onbiometrics, identity managementsystems, and identification cardsand readers is seemingly justaround the corner ? but the greatestbursts of activity have not yetoccurred."The agencies and Congress aretrying to push these programs fullspeed ahead, but there have been afew bumps in the road," saidJeremy Grant, senior vice presidentof Stanford Group Co.'s investmentresearch."Things have been moving instages," said Scott Price, vice presidentof homeland security andcivilian solutions at GeneralDynamics Corp. "First, peopleasked, 'Do we need this?' And then? until the ID card programs hadteeth ? no one cared, and therewas evangelizing going on. Now weare getting the cards out."Several powerful forces havebeen converging in recent monthsto nurture public-sector identitymanagement programs and pushthem to maturity such as:"The intersection of identitymanagement with biometrics andsecurity has been in a big boomsince 9/11," said Victor Lee, senioranalyst at the InternationalBiometric Group consulting firm."The market is significantly moreactive than a decade ago. Withregard to performance, things haveimproved tremendously."Spending on the 10 largest U.S.government identity solutions programsis projected to total $7.7 billionfrom 2007 to 2011, accordingto a January report from StanfordGroup. Accelerated growth is projectedfor 2007, 2008 and 2009,with spending peaking in 2009and flattening in 2010 and 2011.An additional $14 billion in internationalgovernment ID card programsand $250 million in statesponsoredidentity solutions isforecast during the period.Although the DefenseDepartment took an early lead inissuing millions of Common Access Cards in the past several years, newID solutions are moving aggressivelyout of the gate, including the StateDepartment's e-Passport and theTransportation SecurityAdministration's Registered TravelerID cards for frequent airline travelers.The intelligence community andthe FBI also have projects in theworks. Last month, ArlingtonCounty and the city of Alexandria inVirginia issued prototypes of theFirst Responder AuthenticationCredential to police, fire and emergencymedical personnel."Growth is being driven by anumber of programs that havebeen in the works for years ? butto date gone nowhere ? and willfinally take off in 2007," Grantwrote in the Stanford Groupreport. Systems integrators willtake a lead role in implementingthe ID card projects, and industryconsolidation and pressure toreduce prices will continue as alarge number of companies vie fora finite number of programs.The largest program, deploymentof government employee ID cardsunder Homeland SecurityPresidential Directive 12, achievedmilestones in late 2006 but hassince slowed in momentum, in partbecause of a lack of interoperabilityamong vendors' cards. But industryexecutives are optimistic that thoseissues will be resolved."We believe there is tremendouspotential in the HSPD-12 market,"said Jon Rambeau, director of credentialingsystems at LockheedMartin. "FIPS-201 is a phenomenalstandard, and that is driving downthe price."Even so, Grant and others saidthat several major programs ?while moving forward in recentmonths ? have experienced significant delays because of technicalglitches and policy and fundingimpasses, and they have not yetbegun accelerated growth. Forexample, the Real ID Act of2005, which will standardizestate driver's license programs,has faced numerous objectionsfrom state governments overits costs and possible impacton privacy. On March 2,Congress delayed by 20months the states' requiredimplementation of the law,until the end of 2009.Other rumblings: The U.S.Visitor and Immigrant StatusIndicator Technology initiativestumbled in creating a programto identify visitors as theyexit the country, and rollout ofthe Transportation WorkerIdentification Credential haslagged because of uncertaintiesabout encrypting the data andchanges in specifications forthe card readers. Harbor operatorsbalked because they didnot want to manage complexencryption keys, and theyinsisted on a contactless reader."The problems have notbeen solved yet, but in myopinion, they will be able toencrypt the data," said WalterHamilton, chairman of theInternational BiometricIndustry Association.Meanwhile, LockheedMartin, which won the TWICenrollment and card-issuingcontract in January, is workingwith the maritime industryand TSA to ensure compatibilityonce the reader design ismade final.The People Access SecurityServices border-crossing cardexperienced a setback afterHomeland Security SecretaryMichael Chertoff revealed thatthe long-distance RFID chipfailed to perform adequatelyin field tests on a similar IDdocument. Industry sourcessaid the failures are likelybecause of faulty placement ofthe readers rather than thechip technology."The technical solution inthe PASS card is still laggingbehind the need," Price said.Also affecting momentum isthe new, DemocraticCongress, which is increasingoversight on federal contracting at the same time it is scrutinizingthe Iraq War budget.And privacy advocates areopposed to huge expansions inbiometric cards and centralizeddatabases because theyopen the door to invasive governmentsnooping. JimHarper, director of informationpolicy studies at the CatoInstitute, said a government-controlledID system willthreaten privacy and civil liberties.For example, DHS regulationsfor the Real ID Actlay the groundwork for racialtracking, Harper said."The bar code system standardthat DHS calls for in theregulation includes machine readableinformation aboutrace and ethnicity. This isdeeply concerning andunwise," Harper told a congressionalcommittee onMarch 26.Nonetheless, industry executivesare optimistic that identitymanagement technologyoffers substantial benefits inprotecting and verifying identities,and that privacy concernscan be resolved. Niche opportunitiesalso abound in sellingnetworking services, middleware,public-key infrastructuresand federated identitymanagement services.For example, there areopportunities in providing themiddleware for HSPD-12 solutionsand in upgrading thebackbone networks to combinephysical and cybersecurity, saidGreg Gardner, vice president ofgovernment and homelandsecurity solutions at OracleCorp.The challenge is that thecybercomponents typically arerun by the chief informationofficer while the physical accesssystems are run bybuilding security directors, andthere is little integrationbetween them, he said.Another area of growth is infederated identity management,in which infrastructuresare created so a single ID cardcan be used at different agencies.This usually requires linkingthe networks."What really resonates isthat the federated capability issimple and easy to implement,"Gardner said. "The other partsof HSPD-12 are harder toimplement."Despite the challenges, identitymanagement continues tobe a burgeoning field."A year ago, people werescrambling. There was no realfunding and a lot of churn inthese programs," said IvanHurtt, director of federal solutionsat Novell Inc. "Now peopleare rolling out the enrollmentand beginning deploymentof the cards. People reallysee the value of it."
FOLLOW THE MONEY
A BUMPY RIDE
PROTECTING PRIVACY
Staff Writer Alice Lipowicz can be
reached at alipowicz@1105govinfo.
com.
- Urgent need for physical and
cybersecurity since the Sept. 11,
2001, terrorist attacks. - Serious interest in authenticating
identities and protecting
against identity theft. - Technology advancements in
biometrics, radio frequency identi-
fication and smart cards. - Development of Federal
Information Processing Standard
201 and other standards. - Major investments in identity
solutions by large systems integrators
including Lockheed Martin
Corp., General Dynamics Corp.,
Northrop Grumman Corp., EDS
Corp., Maximus Inc., BearingPoint
Co. and Unisys Corp.
FOLLOW THE MONEY
A BUMPY RIDE
PROTECTING PRIVACY
Staff Writer Alice Lipowicz can be
reached at alipowicz@1105govinfo.
com.

